Intrusion Analysis and Prevention
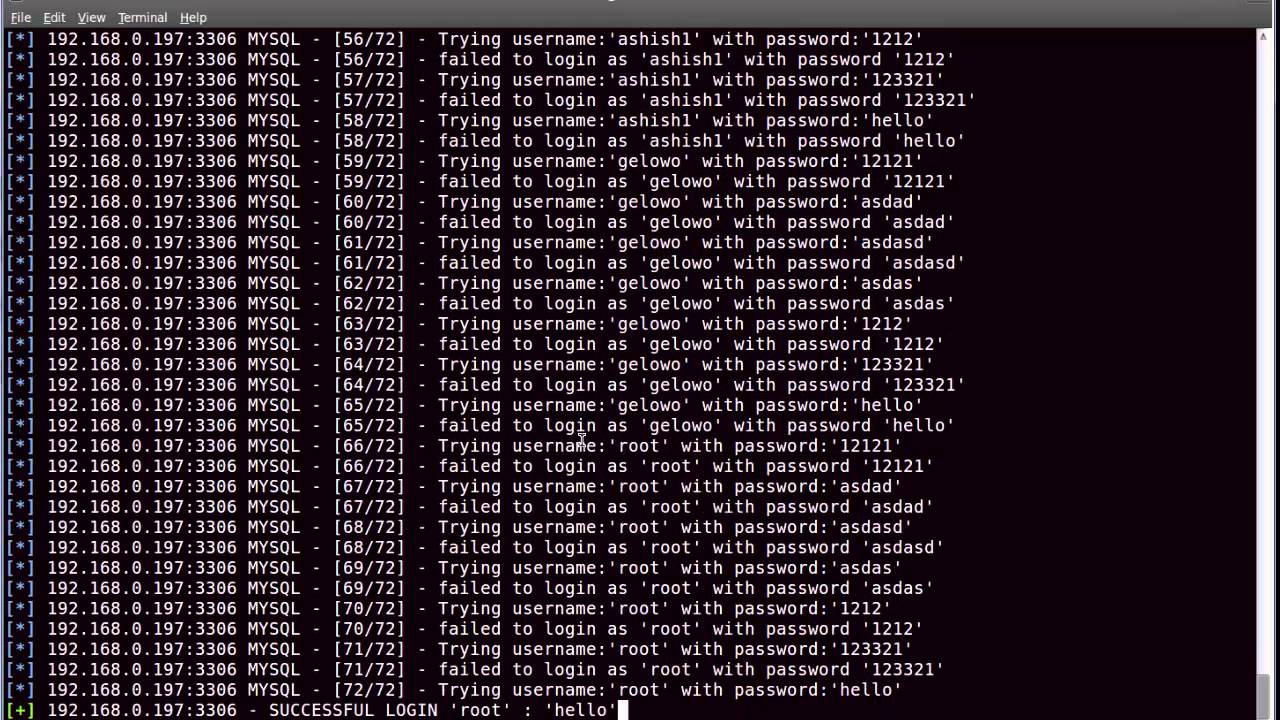
Recovering from a compromised infastructure can be difficult when analyzing damage and ensuring no dangerous malware has been left behind. a2b has extensive experience helping clients analyze the results of unauthorized system entry, including but not limited to root SSH access, unauthorized SQL queries, web server hijacking, cryptolockers (Bitcoin ransom), and more.
a2b professionals will provide a detailed analysis of existing security risks, and guide you through the processes of prevention and recovery.